AI-Powered Threat Prevention for Modern Enterprises
Detect, analyze, and neutralize security threats in real-time with AI-driven insights. Maintain continuous compliance readiness while gaining complete visibility into your risk landscape.

Security Teams Face These Challenges Every Day
Data Breaches
Expanding attack surfaces lead to costly security incidents and reputational damage.
Compliance Pressure
Regulatory requirements grow more complex, making audit readiness increasingly difficult.
Lack of Visibility
Critical blind spots across system, network, and user activity leave you exposed.
Manual Audits
Long tasks and mistakes made by people cause delays and rule-breaking gaps.
Enterprise Security That Works Around the Clock
Our AI-powered platform continuously monitors your infrastructure, detects threats in real-time, and prioritizes risks based on business impact—all without manual intervention.
AI Detects Threats
Our advanced AI continuously monitors your entire infrastructure, identifying vulnerabilities, suspicious activities, and potential security threats in real-time across all endpoints and networks.
Risks Are Prioritized
Intelligent machine learning algorithms automatically rank and categorize threats by severity level, business impact, and urgency, ensuring your team focuses on what matters most.
Incidents Are Resolved
Automated response systems and guided remediation workflows quickly neutralize threats, containing incidents before they escalate and minimizing potential damage to your organization.
Compliance Stays Ready
Maintain continuous compliance with automated audit trails, detailed reporting, and real-time documentation that keeps you ready for any regulatory review without manual effort.
Enterprise Security, Built for Scale
Comprehensive security features designed to protect your infrastructure, ensure compliance, and provide complete visibility across your organization.
Threat Detection
Real-time threat identification across your entire infrastructure with AI-powered anomaly detection and behavioral analysis.

Vulnerability Scanning
Continuous automated scanning of networks, applications, and cloud infrastructure to identify security weaknesses before exploitation.

Identity & Access
Zero-trust identity management with multi-factor authentication, single sign-on, and real-time access monitoring.
Automated Response
Reduce your mean time to resolution with automated playbooks that execute containment actions the moment a threat is verified.
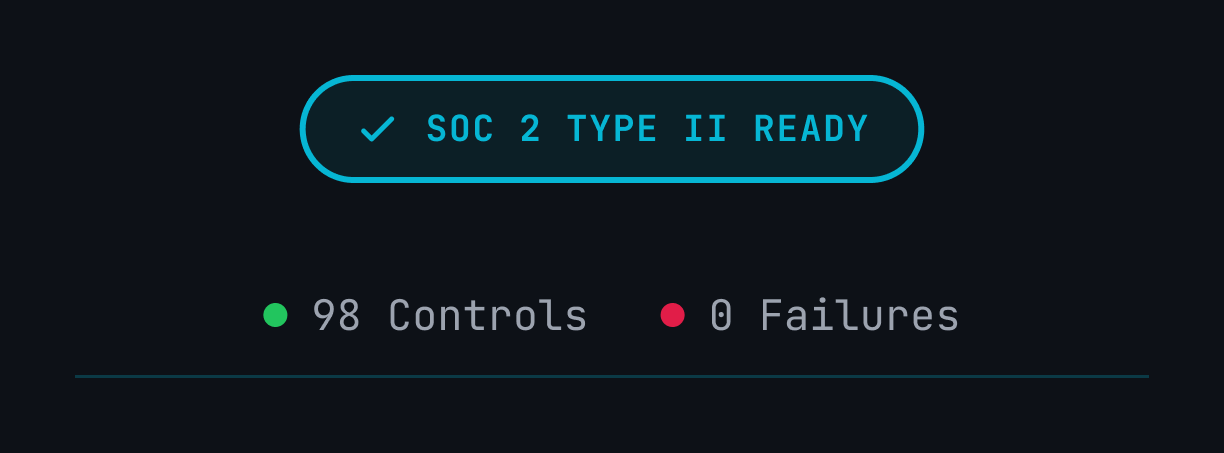
Compliance Tracking
Continuous monitoring against major frameworks like SOC 2, HIPAA, and GDPR with automated evidence collection for every requirement.
Security Intelligence
Gain deep insights into your security posture with advanced analytics that correlate events across different layers of your stack.
Fully Integrated
All capabilities in sync
360° Protection
Complete attack surface
Real-Time
Instant threat detection
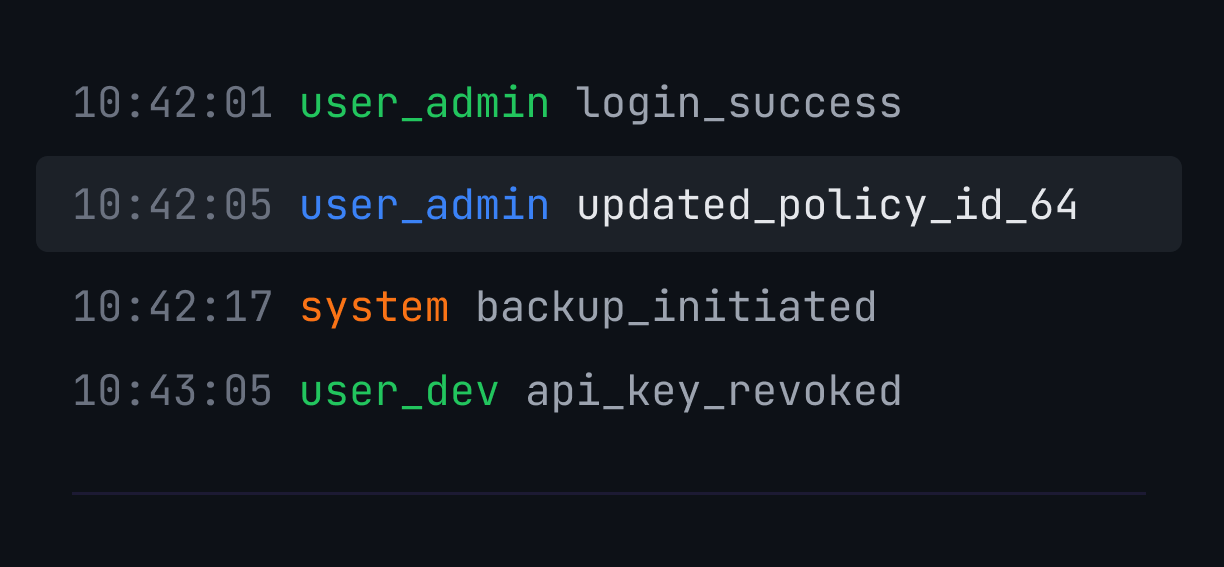
Real-Time Visibility Into Security Risk
Continuously evaluate threats based on likelihood and business impact. Our AI-powered risk engine automatically categorizes and prioritizes vulnerabilities, giving your team instant clarity on what matters most.
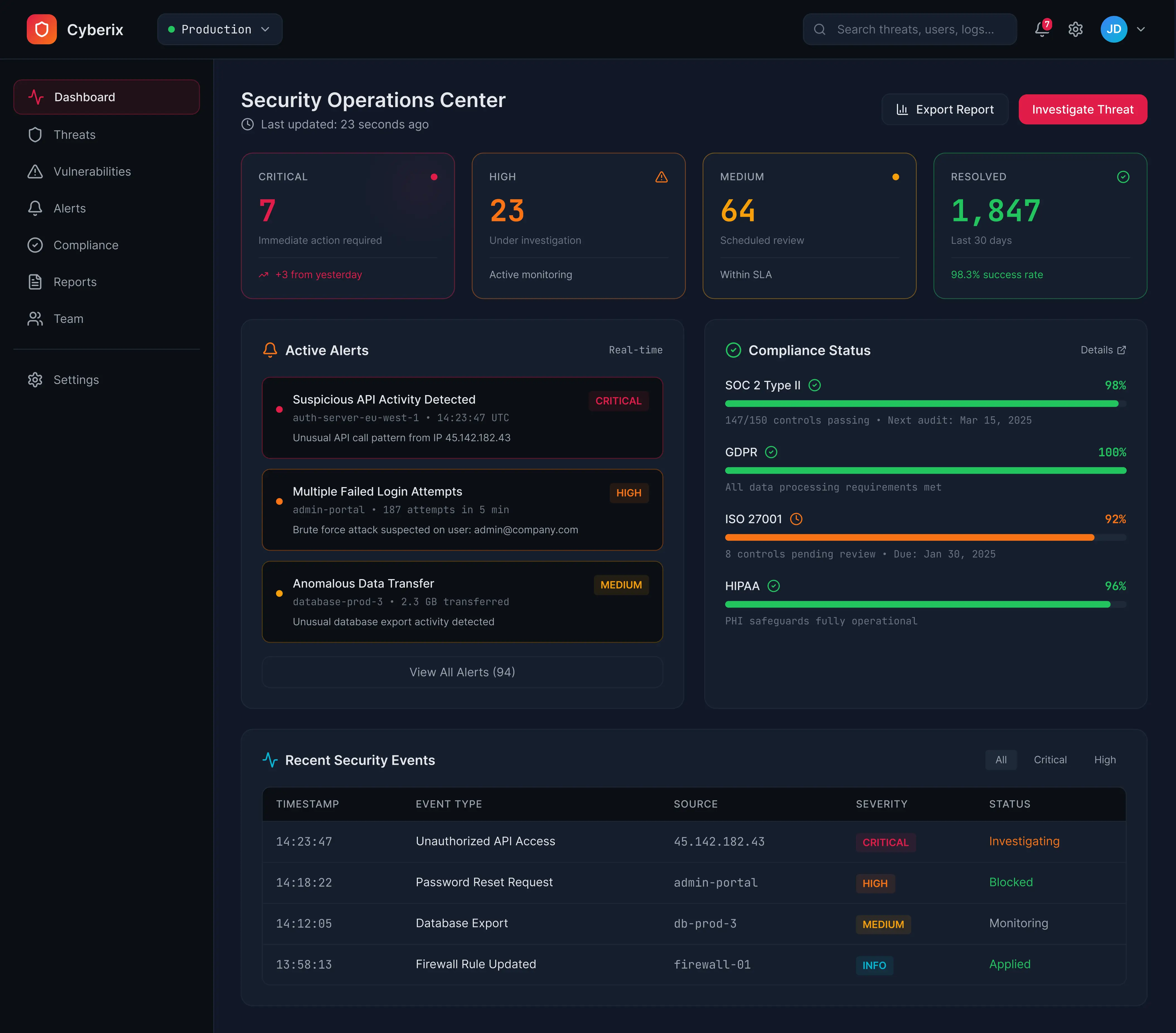
Enterprise-Grade Security Operations in One Dashboard
Real-time visibility across threats, alerts, and compliance.
Integrates Seamlessly With Your Existing Tools
Transform fragmented security operations into a coordinated, automated response system.
Integrations turn fragmented workflows into a single, coordinated response.
Always Audit-Ready, Without the Manual Work
Continuous compliance monitoring with automated evidence collection and verification.
How AI Supports Real Security Decisions
AI assists teams with detection and prioritization and learning by analyzing activity, producing actionable signals, and adapting to your environment.
AI-Driven Detection
-
User behavior
-
Network activity
-
System and access logs
-
Anomaly signals
-
Early threat indicators
Helps teams identify suspicious activity that rule-based systems may miss
Predictive Threat Analysis
-
Historical incidents
-
Current risk signals
-
Trend patterns
-
Risk scores
-
Early warnings
Allows teams to prioritize risks before incidents escalate
Continuous Learning Models
-
Ongoing outcomes
-
Analyst feedback
-
Environmental changes
-
Updated detection logic
-
Improved prioritization accuracy
Reduces manual tuning and keeps detection relevant over time
AI-Driven Detection
-
User behavior
-
Network activity
-
System and access logs
-
Anomaly signals
-
Early threat indicators
Helps teams identify suspicious activity that rule-based systems may miss
Predictive Threat Analysis
-
Historical incidents
-
Current risk signals
-
Trend patterns
-
Risk scores
-
Early warnings
Allows teams to prioritize risks before incidents escalate
Continuous Learning Models
-
Ongoing outcomes
-
Analyst feedback
-
Environmental changes
-
Updated detection logic
-
Improved prioritization accuracy
Reduces manual tuning and keeps detection relevant over time
Built for Security Teams Across Critical Industries
Different industries face different security challenges. Explore how our platform adapts to your environment.
Security Teams Trust Us in Real-World Environments
"Implementing it gave us immediate visibility into lateral movement without the usual configuration overhead. It simply works, allowing our SOC to focus on remediation rather than tuning."

Ready to See the Platform in Action?
Book a personalized demo with our security team and see how Cyberix adapts to your infrastructure.
Request a Demo